Internal networks exposed: Mailpit testing tool under attack
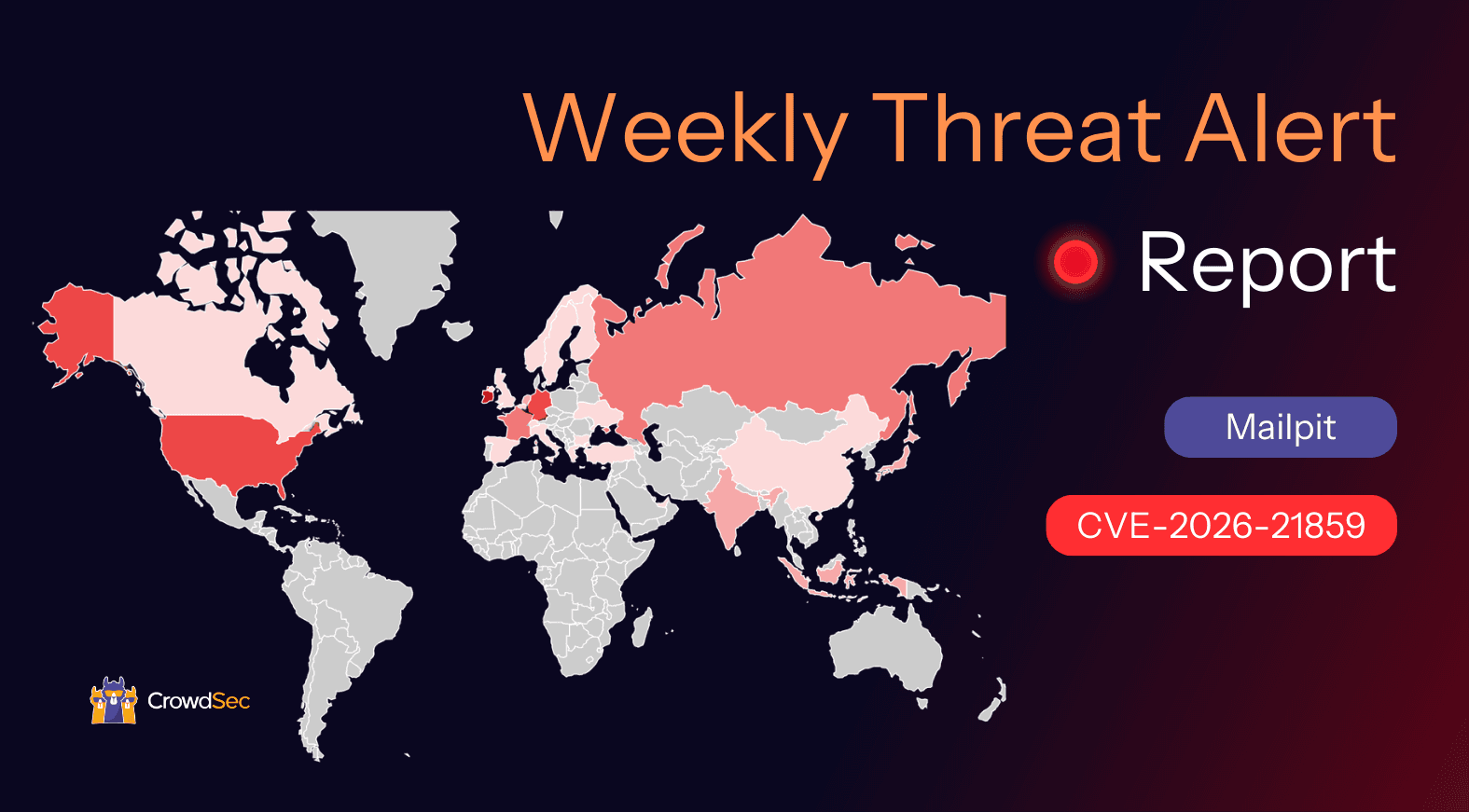
Server-Side Request Forgery (SSRF) is not the most common attack vector, yet it can have a severe impact when targeted at a core tool in your infrastructure. The CrowdSec Network has detected a wave of exploitation attempts targeting CVE-2026-21859, a critical SSRF vulnerability in Mailpit.

Key findings
- CrowdSec first detected exploitation attempts targeting this vulnerability on February 11, 2026.
- Attacks observed so far are highly selective and intelligence-driven, suggesting that threat actors are conducting sophisticated reconnaissance.
- More than 130 IPs have been reported until now, with a clear uptick in malicious activity over the past week as awareness of the vulnerability grows.
What is Mailpit?
Mailpit is a popular email testing tool and API for developers, designed to capture emails sent by applications during development and testing phases. It is widely used by software engineering and QA teams to verify email workflows without sending actual messages to real users.
Why it matters: While Mailpit is a development tool, it is often deployed in environments with access to other internal services. If exposed, this vulnerability turns Mailpit into a gateway for attackers to bypass firewalls and access sensitive internal infrastructure that would otherwise be unreachable from the internet.
How does CVE-2026-21859 work?
This vulnerability is a Server-Side Request Forgery (SSRF) flaw in Mailpit versions 1.28.0 and below. The issue lies in the /proxy endpoint, which is intended to proxy requests but fails to properly validate the destination monitoring.
Attackers can exploit this by sending crafted HTTP GET requests to the /proxy endpoint with a url parameter targeting internal IP addresses (e.g., 127.0.0.1 or internal metadata services). Because the application does not block internal destinations, it executes the request on behalf of the attacker, returning the response from the internal service. This allows unauthorized mapping of internal networks and potential access to sensitive data.
The vulnerability was fixed in version 1.28.1.
Threat Landscape Analysis
CrowdSec data indicates that exploitation of CVE-2026-21859 is currently targeted. Attackers are not spraying the entire internet; instead, they use advanced reconnaissance to identify vulnerable Mailpit instances. This behavior is typical of sophisticated campaigns or advanced persistent threat (APT) operations looking for an initial foothold or lateral movement opportunities.
The recent increase in attack volume suggests that the window for patching is closing as more threat actors incorporate this exploit into their toolkits.


How to protect your systems
- Patch immediately: Update your Mailpit instances to version 1.28.1 or later. This version includes the necessary fixes to validate and restrict the
/proxyendpoint. - Stay Proactive: If you are running Mailpit behind a web server or reverse proxy, ensure the CrowdSec AppSec component is enabled to block malicious request patterns.
- Blocklists: Subscribe to the CrowdSec Community Blocklist to preemptively block known malicious IPs that are scanning for this vulnerability.